Replication TAPs
The most effective way to monitor your copper networksThat crucial network segment’s traffic could then be monitored by an intrusion detection system (IDS), recorded for later forensic examination, captured for future use, or analyzed for performance issues. This type of TAP is useful when a critical segment needs to be monitored by an array of security and compliance tools simultaneously.
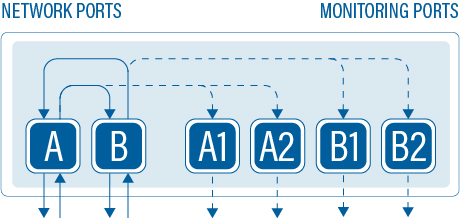
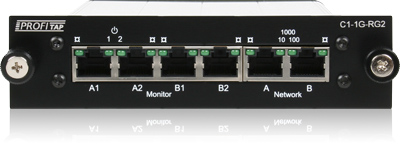
Dual Output Gigabit Copper TAP
Our Dual Output Copper TAP copies the traffic from one network link and outputs it twice.
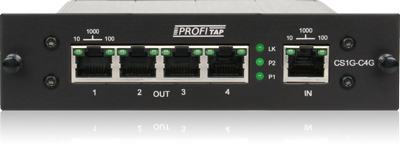
Gigabit Copper Port Replicator
Designed for optimizing mirrored port usage, the Port Replicator receives traffic on 1 port, and replicates it to 4 output ports.
JOIN THE CONVERSATION
Find us on one of the following social platforms to get a sneak peek into the network monitoring world.
BE PART OF THE TEAM
We are always on the lookout for talented and passionate people, who are open to change and innovation.
OUR BLOG
Find the latest insights on network monitoring & analysis so you know which solution suits you best.