Packet forensics solutions
Discover moreData is evidence
Packet capture plays a vital role in digital forensics, lawful interception, and incident response, providing evidence that forms the basis of decision-making in network defense.
Our deep network observability solutions enable you to capture, analyze, and interpret network traffic with forensic precision. This empowers your organization to uncover hidden threats, resolve incidents, and maintain compliance.
Packet-level visibility is essential for packet forensics because it allows for the detailed analysis of individual packets within a network. This level of visibility provides crucial information about the source and destination of each packet, as well as its contents and any potential alterations or manipulations.
Tracing network packets
Detailed packet visibility allows forensic analysts to track the path of a specific packet throughout the network and identify any suspicious activity or potential security breaches. They can also reconstruct the sequence of events leading up to an incident, such as a cyber attack or data breach. By examining the headers and payloads of these packets, they can uncover critical details and clues that may have otherwise gone undetected.


Lawful interception
Using network TAPs to capture packet data offers evidence-based data for incident response and forensic investigations. When a network incident, like an advanced persistent threat (APT), occurs, captured trace files are used to reconstruct events leading up to it, offering valuable insights into the root cause. In legal cases involving cybercrimes, packet forensics provides irrefutable evidence of malicious network activities.
This evidence can be used in court to prosecute cybercriminals for their actions.
In the context of legal frameworks, such as the Communications Assistance for Law Enforcement Act (CALEA), and the European Telecommunications Standards Institute (ETSI) Standards, network TAPs can be used to facilitate the legal intercept of electronic communications, ensuring that law enforcement agencies can access the data they are legally authorized to obtain in real time.
Secure TAPs
TAPs provide a secure and reliable way to intercept data without any risk of being detected or tampered with by the target system. They allow for a non-intrusive method of capturing network traffic without disrupting the flow of data and provide high-quality data with correct timing. This is crucial for maintaining the integrity of the investigation and ensuring that collected evidence can be used in court.

Enhancing forensics capabilities
Focussing on reliable packet capture and actionable network insights, the Profitap unified visibility platform offers powerful tools that enable the investigation and mitigation of potential security incidents.
Profitap traffic access and data optimization solutions enhance forensics capabilities with reliable data for lawful interception and forensics purposes. This allows users to analyze network traffic in real time, providing valuable information on potential threats and malicious activity. If a security threat is not picked up instantly, the captured packet data can be used for incident reconstruction and historical analysis.
Profitap offers full integration with other security tools, such as Network Detection & Response (NDR), IDS/IPS systems, and threat intelligence platforms. This allows for a comprehensive approach to forensic investigations and enables faster response times to potential threats.
Profitap’s network monitoring capabilities provide organizations with powerful tools to investigate and mitigate potential security incidents.

Profitap Network TAPs
Profitap Network TAPs are hardware devices that provide fail-safe access to the complete network traffic of the network connection in which they are deployed. Profitap TAPs offer a range of features, including high-speed and low-latency data capture, advanced filtering capabilities, and support for various network interfaces. These TAPs ensure that all network traffic is reliably forwarded to the next component in the solution stack.
- Non-intrusive in-line network access to ALL data.
- Permanent network link guaranteed.
- Passive, unpowered (fiber).
- Protect network link availability for in-line security tools.
- Deliver lossless traffic aggregation from multiple in-line links or out-of-band connections (Booster series).

Network Packet Brokers (NPBs)
Network Packet Brokers are intermediaries between network TAPs and monitoring or security tools. They receive the captured network traffic from TAPs and optimize it before distributing it to the appropriate monitoring devices. NPBs provide traffic aggregation, filtering, load balancing, timestamping, and deduplication features. These capabilities optimize the utilization of monitoring tools and enhance scalability, allowing organizations to monitor network traffic efficiently.
- High throughput.
- Traffic optimization (Aggregation, Load Balancing, Filtering, Timestamping, Deduplication, SSL/TLS Decryption, etc.).
- Flow-aware load balancing across multiple devices.
- Centralized control.
Packet capture and analysis

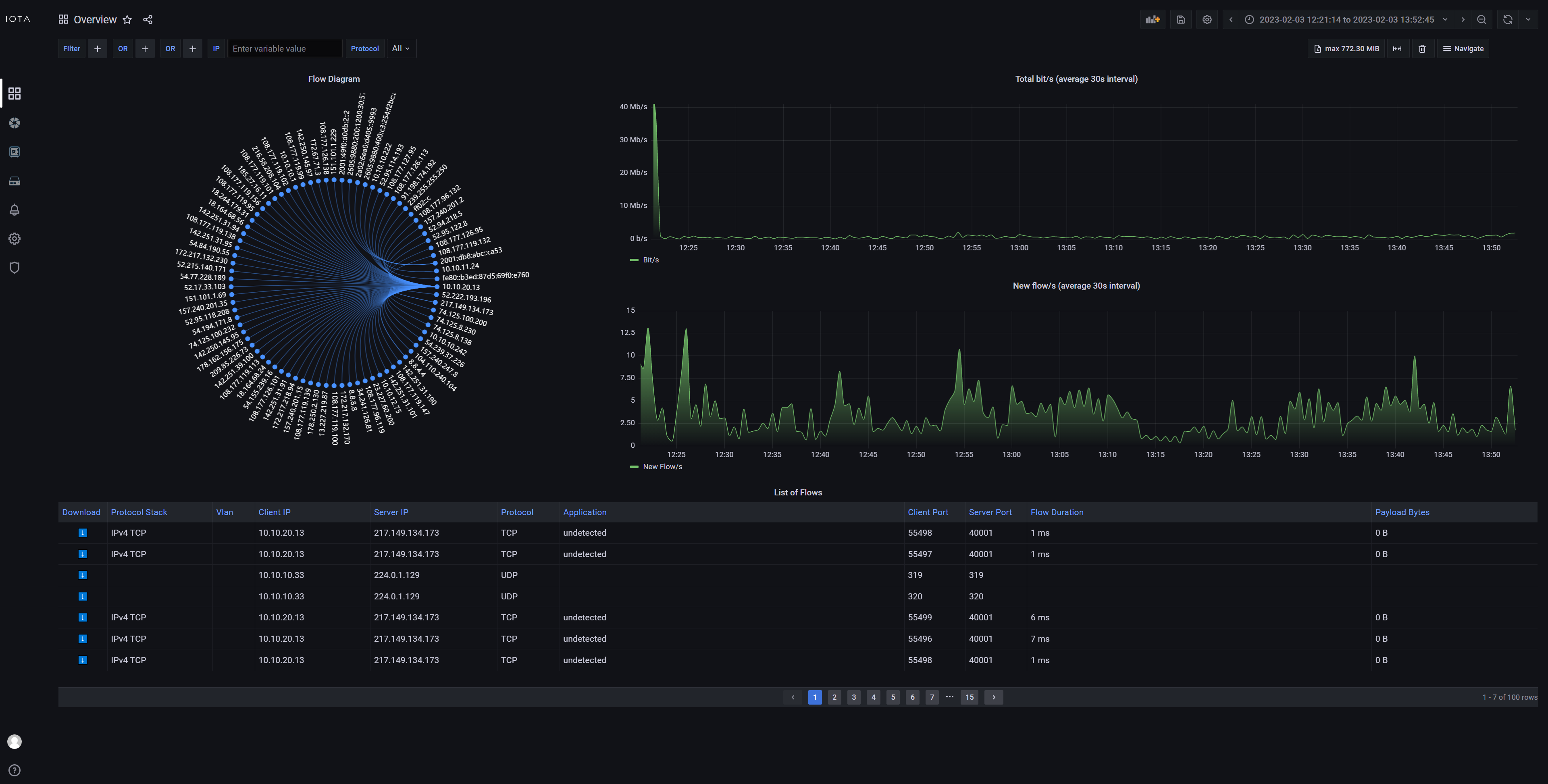
IOTA EDGE
- Deployed on edge and remote sites.
- Integrated analysis dashboards accessible locally or remotely.
- In-line or out-of-band.
- 1 TB or 2 TB capture storage.
- Capture performance 3.2 Gbps.

IOTA CORE
- Deployed on central capture point.
- Integrated analysis dashboards accessible locally or remotely.
- Out-of-band.
- 4, 8, or 16 TB capture storage.
- Capture performance 20 Gbps.

Centralized management application
- Central interface for bird’s-eye view insight into IOTA analytics.
- Fleet management and maintenance.
- Multi-segment analysis: Latency measurement between different capture points for edge IOTAs.
Resources
Application latency analysis
More and more applications are provided by cloud providers as SaaS from globally distributed data centers. Normally, this offers easy application deployment. However, it also brings new error…
Troubleshooting DNS
There is a saying: “It’s not DNS. There is no way it’s DNS. It was DNS”. This makes it clear that DNS is an integral part of IT infra-structure services and can exhibit a wide variety of error…
Network monitoring in virtual and physical multi-tenant networks
A multinational technology company specialized in cloud communications and workstream collaboration solutions with multiple global sites tasked Profitap to design a constant and…